No jargon, no panic — just what you actually need to know about the digital dangers shaping this year.
You don’t need to be a tech expert to be a target. In 2026, cybercriminals are smarter, faster, and more creative than ever — and they’re going after everyday people, small businesses, and giant corporations alike. This guide breaks down the biggest threats in plain language, so you can actually understand — and protect yourself from — what’s out there.
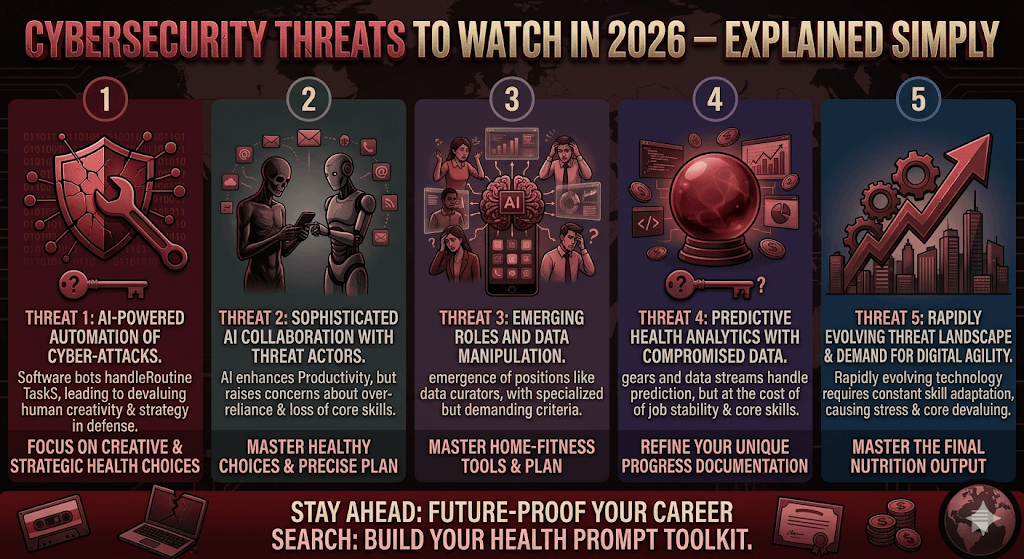
AI-Powered Attacks: When Hackers Get a Supercharger
Imagine giving a cyber criminal access to the smartest assistant in the world — one that never sleeps, never makes grammar mistakes, and can write a convincing fake email in 30 seconds flat. That’s essentially what’s happened with AI.
In 2026, attackers are using artificial intelligence to scale up phishing, automate hacking attempts, and craft messages so personalized they’re almost impossible to spot as fake. The old tells — weird spelling, awkward phrases — are largely gone.
According to IBM’s X-Force 2026 report, AI has lowered the bar dramatically for would-be attackers — meaning you no longer need technical skills to launch a sophisticated cyberattack. You just need access to the right tools.
Think of it like this: before AI, running a scam required skill and time. Now it’s like going from handwriting a thousand fake letters to printing a million of them overnight.
What you can do: Be skeptical of any unexpected message asking you to click a link or provide information — even if it looks completely real. When in doubt, call the sender directly using a known number.
Ransomware 3.0: Held Hostage, Publicly Shamed
Ransomware is the digital equivalent of someone breaking into your home, locking all your stuff in a safe, and demanding money for the combination. But in 2026, the attacks have evolved to be even crueler.
Today’s ransomware gangs don’t just encrypt your files — they steal them first. Then they threaten to publish your private data publicly if you don’t pay up. This “double extortion” model has become the standard playbook, and ransomware now accounts for over half of all global cyberattacks.
In early 2026, Stryker — a major medical device manufacturer — had to restore most of its manufacturing operations after a crippling ransomware attack. These aren’t abstract threats; they shut down real businesses and real services.
Who’s most at risk?
Hospitals, schools, local governments, and small businesses tend to be prime targets because they often have outdated systems and limited IT staff. But no organization is immune.
What you can do: Keep regular backups of important files stored offline or in a secure cloud. If ransomware hits, backups mean you don’t have to pay to get your data back.
Supply Chain Attacks: Hacking the Trusted Middleman
You lock your front door, but what if the plumber who comes to fix your pipes has a copy of your key? That’s the logic behind supply chain attacks — hackers don’t go after their real target directly. Instead, they compromise a trusted third-party vendor first.
IBM’s X-Force 2026 report found that major supply chain breaches have quadrupled over the past five years. A recent example involved attackers using compromised OAuth tokens from a smaller platform to quietly access much larger corporate environments — all without triggering any alarms.
These attacks succeed because organizations inherently trust the tools and services they’ve integrated into their workflows. By the time anyone notices, attackers may have had access for months.
It’s like contaminating a water supply upstream rather than breaking into every individual house. One compromise, thousands of victims.
What you can do: If you’re a business owner, ask your vendors about their security practices. Don’t assume that because a tool is popular, it’s safe. Vet your digital supply chain the same way you’d vet a financial supplier.
Identity Theft Gets Smarter: Deepfakes & Voice Cloning
In 2026, “seeing is believing” is no longer a safe rule. Deepfake technology has matured to the point where realistic fake videos and voice clips can be generated in minutes. Criminals are using these to impersonate executives, trick employees into wiring funds, or bypass voice-based authentication.
According to Gartner, the rise of AI agents is also complicating identity management for organizations — creating new challenges around who (or what) is actually making a request, and whether that entity should be trusted.
Scammers are now cloning the voices of family members to call elderly relatives in distress, claiming to be in trouble and urgently needing money. These scams are devastatingly effective because they exploit genuine emotional bonds.
The “AI agent” problem
As more companies use AI agents to automate tasks — booking meetings, sending emails, managing files — attackers have a new avenue: compromise the agent, and you compromise everything it has access to. Traditional security tools weren’t built with this in mind.
What you can do: Agree on a private “safe word” with close family members for emergency calls. For businesses, establish verification protocols that go beyond voice or video calls for sensitive transactions.
The Quantum Countdown: Harvest Now, Decrypt Later
This one sounds like science fiction, but it’s an active concern for governments and security experts worldwide. Quantum computers — which process information in fundamentally different ways than today’s machines — will eventually be able to crack the encryption that protects most of our sensitive data.
The scary part? Attackers are already stealing encrypted data right now, banking on decrypting it in the future when quantum computers are powerful enough. Gartner predicts current encryption methods could become unsafe by 2030.
Health records, financial data, government secrets — anything encrypted and stored today is potentially vulnerable tomorrow. The transition to quantum-safe encryption needs to start now, not in five years.
Think of it like stealing a locked diary today, knowing you’ll find the key sometime next decade. The theft happens long before the reading does.
What you can do: If you work in an industry handling long-term sensitive data (healthcare, law, finance), start asking your IT team about “post-quantum cryptography” migration plans. It’s not too early.
Geopolitical Cyber Wars: Nation-States Enter the Chat
Cybersecurity in 2026 isn’t just about criminals chasing money. Nation-state actors — governments using cyber tools as weapons — are increasingly targeting critical infrastructure, election systems, and private companies to gather intelligence or cause disruption.
The World Economic Forum’s 2026 Global Cybersecurity Outlook identifies geopolitical fragmentation as a key driver reshaping the threat landscape. When international cooperation breaks down, cybercrime flourishes in the gaps.
In early 2026, Lockheed Martin was targeted in an alleged breach by a pro-Iran hacktivist group — a reminder that geopolitical tensions don’t stay in the physical world. They spill into cyberspace too.
What does “widening cyber inequity” mean?
Not all organizations — or countries — can afford the same level of protection. The WEF report warns that as attacks become more sophisticated, the gap between those with strong defenses and those without is growing. Smaller businesses and developing nations are left especially exposed.
What you can do: Support legislation and organizations that push for stronger international cyber cooperation. At a personal level, be aware that your data held by companies operating in geopolitically sensitive sectors may face elevated risk.
The Bottom Line: Knowledge Is Your First Defense
Cybersecurity doesn’t have to be overwhelming. The threats are real and evolving — but so are the tools and practices to counter them. The biggest vulnerability in most systems isn’t the software. It’s the gap between what people know and what they do.
You don’t need to become a cybersecurity expert. You need to stay curious, stay skeptical of unexpected requests, keep your software updated, and back up what matters. Small habits, done consistently, stop a huge number of attacks before they start.
The hackers are getting smarter. But so can you.


Comments are closed.