In today’s digital world, the term “hacker” often gets thrown around without much clarity. Movies and news headlines sometimes paint hackers as mysterious villains who break into systems, steal data, or disrupt networks. But the reality is more nuanced. There are distinct categories of hackers, each with different intentions and skill sets. Understanding these differences is essential for anyone interested in technology, cybersecurity, or protecting their digital presence.
In 2026, the word “hacker” gets thrown around in news headlines, movies, and everyday conversations, but most people use it incorrectly. One person calls a cybercriminal a “hacker,” while another praises a security expert as a “hacker.” Then there’s “cracker,” a term that feels outdated to some but still appears in textbooks and discussions.
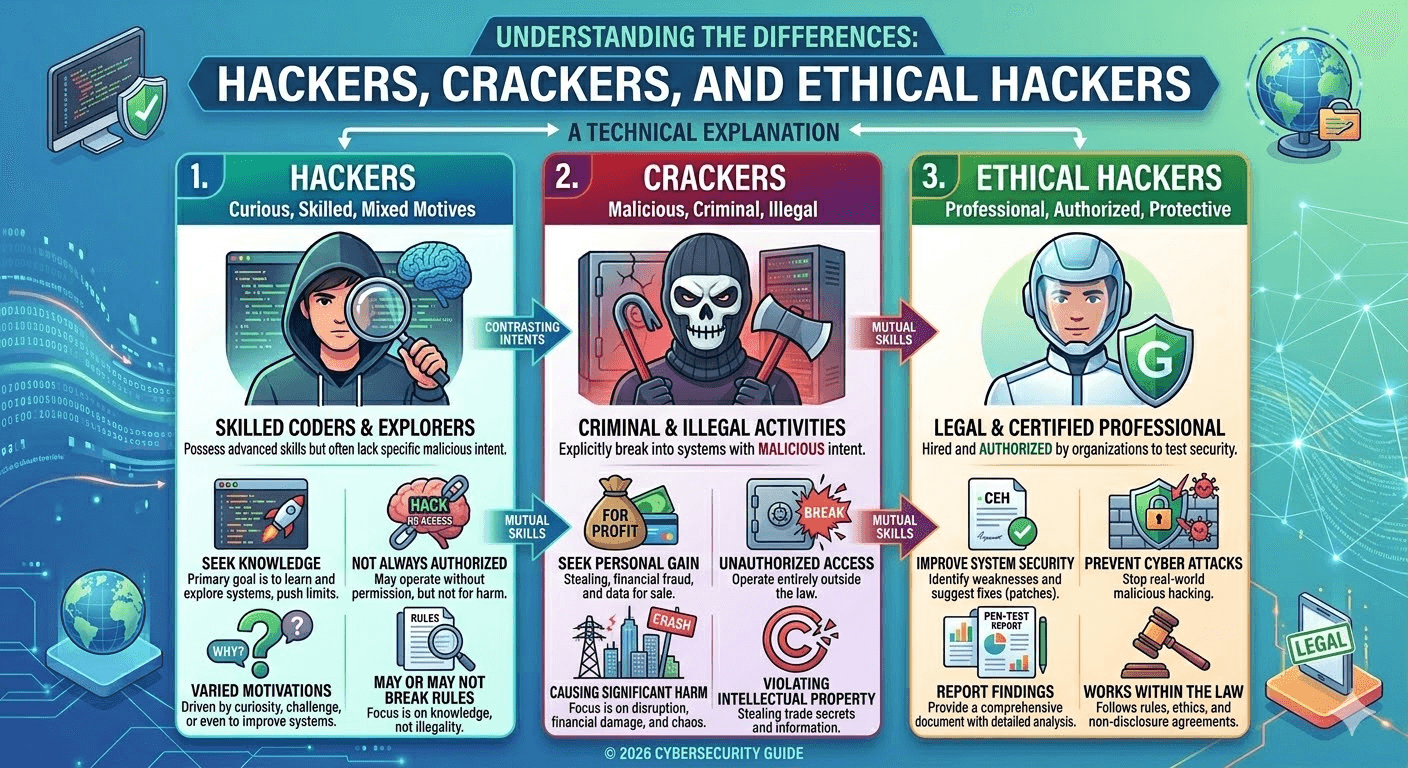
The confusion is real—and it’s important to clear it up. Understanding the differences between hackers, crackers, and ethical hackers helps you separate myth from reality in cybersecurity. It also shows why some skilled people defend systems while others attack them.
This guide explains the distinctions in clear, modern terms, based on how professionals, certifications, and the industry actually use these labels today.
The Hat System: The Modern Way We Classify “Hackers”
Today, the cybersecurity community rarely uses “hacker” vs. “cracker” as the primary divide. Instead, we use the “hat” metaphor — inspired by old Western movies where good guys wore white hats and bad guys wore black:
- White Hat → Ethical, legal, protective
- Black Hat → Malicious, illegal, destructive
- Gray Hat → In-between, often unauthorized but not always harmful
“Ethical hacker” is now the standard term for white hats. “Cracker” is an older label mostly used to describe black-hat activities, especially those focused on breaking copy protection, cracking passwords, or bypassing software licenses. Many experts consider “cracker” somewhat outdated or narrow—most just say “black hat hacker” or “cybercriminal” in 2026.
In this article, we’ll break down the difference between hackers, crackers, and ethical hackers.
1. Who Are Hackers?
A hacker is someone skilled in computer systems, programming, and networks. Traditionally, a hacker is defined by their curiosity and ability to explore technology, often pushing the boundaries of what is possible. Not all hackers have malicious intent.
A hacker is anyone with advanced technical skills who explores, manipulates, or pushes the limits of computer systems, networks, software, or hardware—often creatively solving problems or finding new ways to use technology.
- Core motivation: Curiosity, innovation, passion for understanding “how things work.”
- Not inherently good or bad — The term is neutral, like calling someone a “driver.” A skilled driver can race legally or rob banks in a getaway car.
- Modern usage: In tech communities (especially open-source, programming, and maker spaces), “hacker” still carries a positive or neutral connotation: life-hacker, growth-hacker, security-hacker.
But in mainstream media and law enforcement, “hacker” almost always implies criminal activity (which frustrates real technologists).
Characteristics of Hackers:
- Deep knowledge of programming languages, operating systems, and networks.
- Ability to identify vulnerabilities in software or hardware systems.
- Often motivated by curiosity, challenge, or innovation rather than personal gain.
Hackers can be further classified based on their intent, which brings us to crackers and ethical hackers.
2. What Are Crackers?
Crackers are hackers who use their skills for malicious purposes. They break into systems without permission, usually to steal data, cause damage, or commit cybercrime. Crackers are the ones that mainstream media often portrays as “hackers.”
Crackers are individuals who deliberately break into systems, crack software protections, decrypt passwords, or exploit vulnerabilities with malicious or illegal intent — usually for personal gain, profit, revenge, or disruption.
- Key traits:
- Unauthorized access
- Harmful outcomes: data theft, ransomware deployment, identity fraud, system sabotage
- Often use pre-made tools or exploits rather than original research
- Why the term “cracker”? It originated in the 1980s–90s to distinguish people who “crack” copy protection on software (warez scene) from true hackers who built things. Many in the community still prefer “cracker” for purely destructive or piracy-focused actors.
- 2026 reality: Most people now lump them under black hat hackers. Black hats include ransomware gangs, state-sponsored spies, cryptojackers, and organized cybercrime rings making billions.
Common Activities of Crackers:
- Breaking passwords to gain unauthorized access.
- Spreading malware or viruses to disrupt systems.
- Stealing sensitive information, such as banking details or personal data.
- Defacing websites or causing intentional downtime.
In short, crackers exploit vulnerabilities for personal gain, financial benefit, or just to cause chaos. Their actions are illegal and punishable under cybersecurity laws.
3. What Are Ethical Hackers?
Ethical hackers, also known as white-hat hackers, use their skills to help organizations strengthen their security. Unlike crackers, ethical hackers have permission to test systems and networks to identify vulnerabilities before malicious hackers can exploit them.
Ethical hackers (also called white hat hackers, penetration testers, or red teamers) use the exact same skills, tools, and techniques as black hats—but with explicit permission, following legal and ethical guidelines to find and fix security weaknesses before criminals exploit them.
- Key traits:
- Always authorized (via contracts, bug bounty programs, or employment)
- Report findings responsibly (to the owner/company)
- Goal: Strengthen defenses, not cause harm
- Common roles in 2026:
- Penetration testers (pentest)
- Bug bounty hunters (paid by companies like Google, Microsoft, HackerOne)
- Red team operators simulating advanced attacks
- Security consultants/certified pros (CEH, OSCP, PNPT holders)
- Certifications & careers: Ethical hacking is a high-demand job. In 2026, roles pay well (often $100K+ starting), with demand exploding due to AI-driven threats, cloud complexity, and ransomware epidemics.
Key Responsibilities of Ethical Hackers:
- Conduct penetration testing to find security weaknesses.
- Advise on security improvements and risk mitigation.
- Simulate cyber attacks to prepare organizations for potential threats.
- Ensure compliance with cybersecurity regulations and standards.
Ethical hacking is legal and highly respected in the cybersecurity industry. Many companies actively hire ethical hackers to protect their digital assets.
4. Hackers vs. Crackers vs. Ethical Hackers: Key Differences
| Feature | Hacker | Cracker | Ethical Hacker |
|---|---|---|---|
| Intent | Can be neutral, curious, or innovative | Malicious, illegal | Protective, legal |
| Permission | Sometimes unauthorized | Always unauthorized | Always authorized |
| Activities | Exploring systems, coding, learning | Breaking systems, stealing data | Testing security, identifying vulnerabilities |
| Legality | Depends on actions | Illegal | Legal and encouraged |
| Outcome | Knowledge gain or innovation | Harm, theft, disruption | Strengthened security, risk reduction |
5. Why Understanding These Differences Matters
In 2026, cybersecurity threats are more sophisticated than ever. Knowing the difference between hackers, crackers, and ethical hackers can help you:
- Protect your personal and business data.
- Recognize potential threats before they escalate.
- Consider a career in cybersecurity as an ethical hacker.
- Avoid mistakenly labeling skilled professionals as criminals.
6. Conclusion
Not every hacker is a villain. Hackers represent skill and curiosity, crackers represent danger and crime, and ethical hackers represent protection and trust. As our lives become increasingly digital, distinguishing between these groups is vital for security, education, and innovation.
If you’re interested in cybersecurity, consider learning ethical hacking—it’s a way to use your tech skills for good, protect data, and even build a rewarding career.
- Hacker = Skilled explorer (neutral term)
- Cracker / Black Hat = Malicious intruder (criminal)
- Ethical Hacker / White Hat = Authorized defender (hero in cybersecurity)
The real divide isn’t skill—it’s intent and permission.
If you’re curious about tech and security, channel that energy ethically: learn penetration testing, join bug bounties, earn certifications. You’ll stay on the right side of the law—and help make the digital world safer.
Three Worlds
- Hackers explore, create, and push boundaries. They are the builders and tinkerers.
- Crackers exploit, steal, and destroy. They are the criminals.
- Ethical hackers defend, test, and secure. They are the guardians.
The next time you hear a news report about a “hacker” breaking into a company, remember: the accurate term is likely cracker or cybercriminal. And the people working around the clock to stop them? Many of them are hackers too—just the kind who use their skills to protect rather than destroy.


