Quantum Computing and the Future of Cybersecurity: The Double-Edged Sword That’s About to Change Everything
Hey there, fellow tech enthusiasts and everyday digital warriors!
Imagine waking up one morning, checking your bank balance, and realizing that the “secure” lock icon on your browser was just a polite suggestion. A powerful quantum computer somewhere just cracked open decades of encrypted data like a cheap padlock. Sounds like sci-fi thriller material, right? But in 2026, this isn’t distant fiction — it’s the very real pivot point we’re speeding toward.
At Inspireviraltimes.com, we love stories that blend jaw-dropping innovation with “what does this mean for me?” moments. Today, we’re diving deep into quantum computing and cybersecurity. I’ll keep it straightforward, skip the jargon overload, and sprinkle in real talk about why this matters to your online life, your business, and our shared digital future. Let’s explore the threats, the breakthroughs, and — most importantly — how we can turn this quantum revolution into a security upgrade instead of a nightmare.
A new era of quantum computing may pose threats closer than we think, Google warns | Euronews
First Things First: What Even Is Quantum Computing?
Let’s start with the basics, because quantum stuff sounds intimidating until you realize it’s just nature showing off.
Your laptop or phone uses bits — tiny switches that are either 0 or 1. Think of a light switch: on or off. Simple.
A quantum computer uses qubits. A single qubit can be 0, 1… or both at the same time (thanks to something called superposition). It’s like a spinning coin that’s heads and tails until you look at it. Add entanglement (where qubits magically link up so changing one instantly affects another, even miles away), and suddenly you have a machine that can explore millions of possibilities at once.
The result? Problems that would take today’s supercomputers longer than the age of the universe become solvable in hours or days. Mind-blowing potential for medicine, climate modeling, and AI. But here’s the flip side that keeps cybersecurity pros up at night…
The Dark Side: When Quantum Computers Become Code-Breakers
Most of the internet’s security today relies on clever math problems that are hard for classical computers: factoring huge numbers (RSA) or solving discrete logarithms (ECC). Your banking app, encrypted emails, VPNs, and even Bitcoin wallets depend on these.
Enter Shor’s algorithm — a quantum trick discovered back in 1994 that turns those “impossible” math puzzles into child’s play for a sufficiently powerful quantum machine. Recent research has slashed the resources needed dramatically; what once required 20 million qubits might now need far fewer.
Google itself just warned that “a future quantum computer can break current encryption” sooner than many expected, and they’re setting an internal migration deadline for 2029. Other experts point to a realistic “Q-Day” window around 2030–2035 when cryptographically relevant quantum computers could arrive.
Worse? The “Harvest Now, Decrypt Later” attack is already happening. Bad actors (and some nation-states) are quietly scooping up encrypted data today and storing it, waiting for the quantum key to unlock it tomorrow. Your old emails, medical records, or corporate secrets? They could be future headlines.
But before you panic and smash your router, let’s talk hope — because quantum isn’t just a villain here. It’s also the hero.

Post Quantum Cryptography Quantum Resistant Cryptography Stock Illustration 2590519703 | Shutterstock
The Quantum Rescue Squad: Post-Quantum Cryptography and Quantum Key Distribution
Good news: the cybersecurity world has been preparing for this exact moment.
1. Post-Quantum Cryptography (PQC) These are brand-new encryption algorithms designed to run on today’s classical computers but resist quantum attacks. In 2024, NIST (the U.S. standards body) released the first official standards:
- FIPS 203 (ML-KEM) for secure key exchange
- FIPS 204 (ML-DSA) for digital signatures
- FIPS 205 (SLH-DSA) as a backup hash-based option And in 2025, they added HQC for even more options.
Governments and big tech are already migrating. Google, Microsoft, and the U.S. Department of Defense have aggressive timelines. The beauty? You won’t notice the switch — it happens under the hood, like a silent software update that makes your digital life stronger.
2. Quantum Key Distribution (QKD) This is the sci-fi cool part. Using the laws of physics themselves, QKD lets two parties share encryption keys that are provably secure. If anyone eavesdrops, the laws of quantum mechanics cause detectable disturbances — like a tamper-proof seal that screams if broken.
Real-world deployments are here now in 2026:
- China’s nationwide quantum network
- Europe’s EuroQCI satellite-fiber project
- Banks and telecoms using ID Quantique, Toshiba, and KETS systems
- Even smartphone-level quantum security pilots
It’s not perfect (distance limits and hardware costs remain), but for ultra-sensitive data like critical infrastructure or diplomatic comms, it’s game-changing.
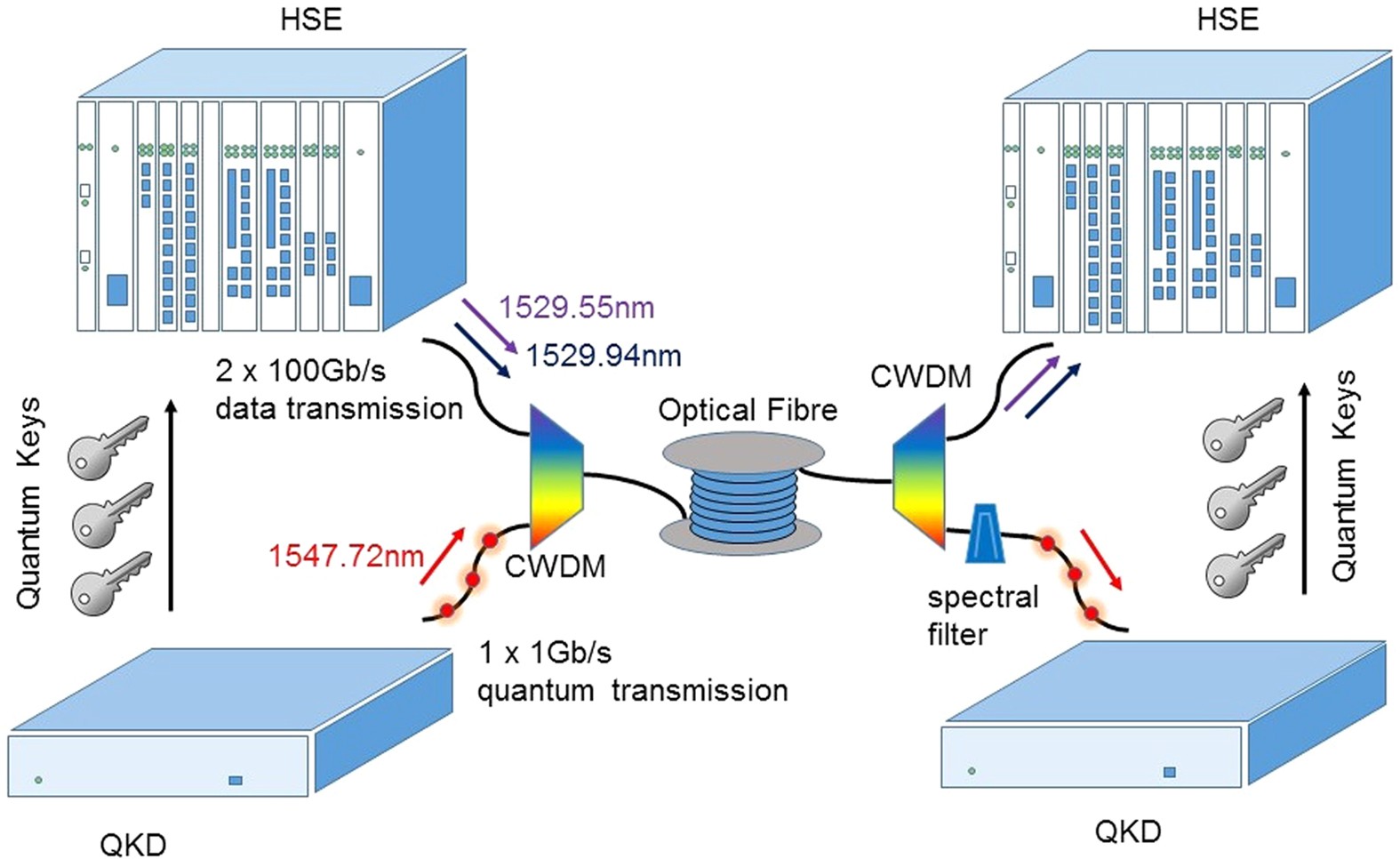
Ultra-high bandwidth quantum secured data transmission | Scientific Reports
Where Are We in 2026? Progress That Feels Like Magic
We’re not waiting for some distant future — the breakthroughs are accelerating right now:
- IBM’s Nighthawk and roadmap to fault-tolerant systems
- Google’s Willow chip crushing error-correction records
- Microsoft’s Majorana 1 topological qubits promising massive scalability
Quantum advantage (where quantum beats classical computers on real problems) is expected to be verified by the end of 2026. Hybrid systems combining quantum and classical power are already in pilot programs for finance, healthcare, and energy.
The message? We’re not helpless spectators. Human ingenuity is meeting this challenge head-on.
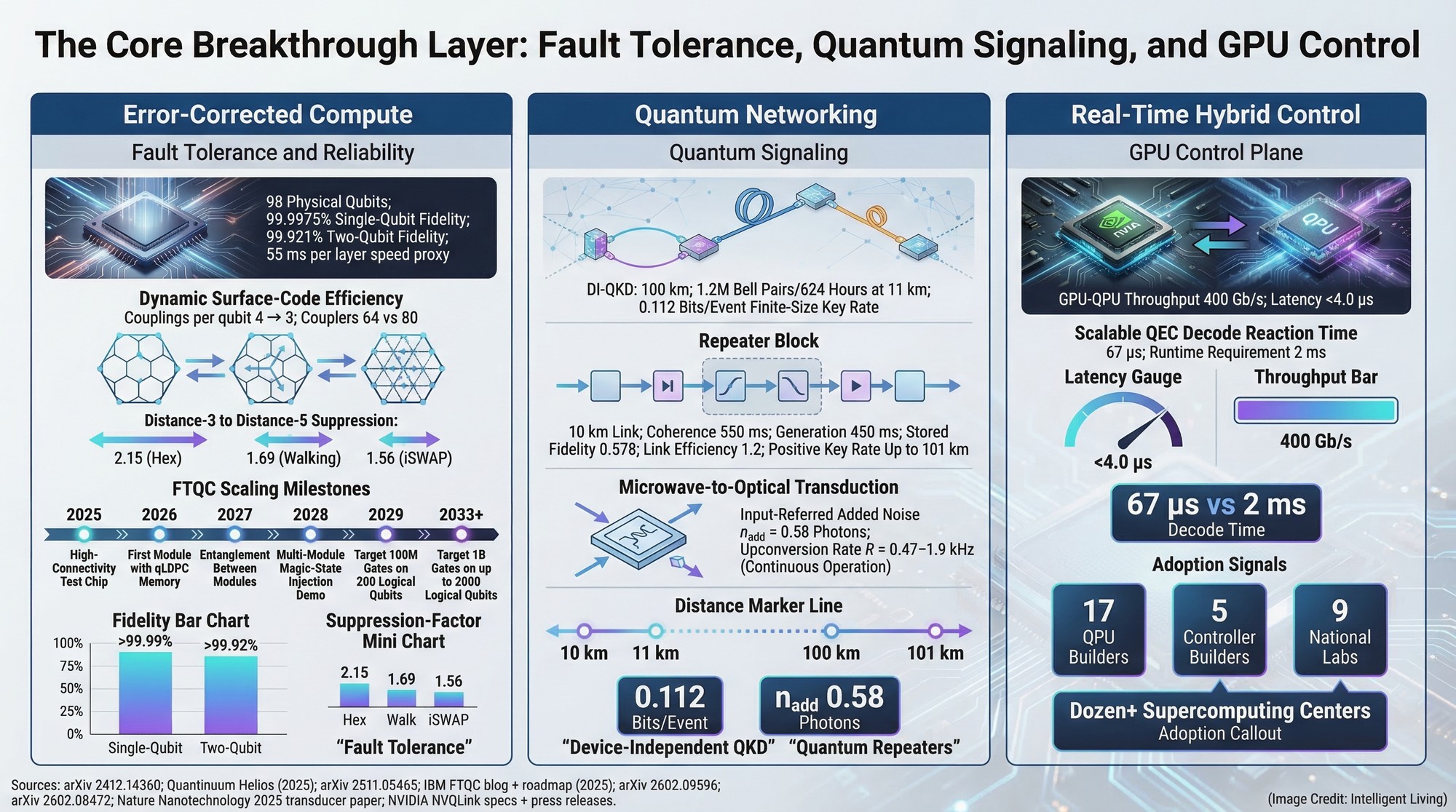
The Quantum Computing Convergence Breakthrough Moment Arrives: 17 Advancements in Error…
So… What Should You Do Right Now?
Don’t wait for the panic headlines. Here’s your practical playbook:
For individuals:
- Use password managers with strong, unique keys and enable passkeys everywhere
- Keep software updated (PQC is rolling out in browsers and apps)
- Support companies prioritizing quantum-safe tech
For businesses & leaders:
- Inventory your cryptographic systems today
- Adopt hybrid PQC + classical encryption (crypto-agility)
- Pilot QKD for high-value links
- Train your teams — this is the new “Y2K” but with way better upside
For everyone: Stay curious. The same quantum tech threatening encryption will also turbocharge drug discovery, climate solutions, and unbreakable privacy tools.
The Inspiring Flip Side: A More Secure Digital Tomorrow
Yes, quantum computing is disruptive. But disruption has always been the birthplace of progress. Just as the internet forced us to invent HTTPS, quantum is pushing us toward cryptography that’s fundamentally stronger — more private, more resilient, and more future-proof.
We’re not heading into a cyber-apocalypse. We’re stepping into an era where security isn’t an afterthought; it’s baked into the physics of the universe.
At Inspireviraltimes.com, we believe the future belongs to those who prepare and innovate together. So bookmark this page, share it with your team, and start the conversation. The quantum era isn’t coming — it’s already knocking. Let’s open the door with confidence, curiosity, and a rock-solid digital shield.
What do you think — excited, nervous, or both? Drop your thoughts in the comments. And if this sparked that “aha!” moment, hit share — because the more we understand this together, the safer (and cooler) our future will be.
Stay inspired, stay secure, and keep looking forward. — The Inspireviraltimes Team
(Sources include official NIST updates, Google’s 2026 cryptography migration timeline, and leading quantum research roadmaps. All data current as of April 2026.)


Comments are closed.